Transforming Your Data into Scalable Predictive Applications
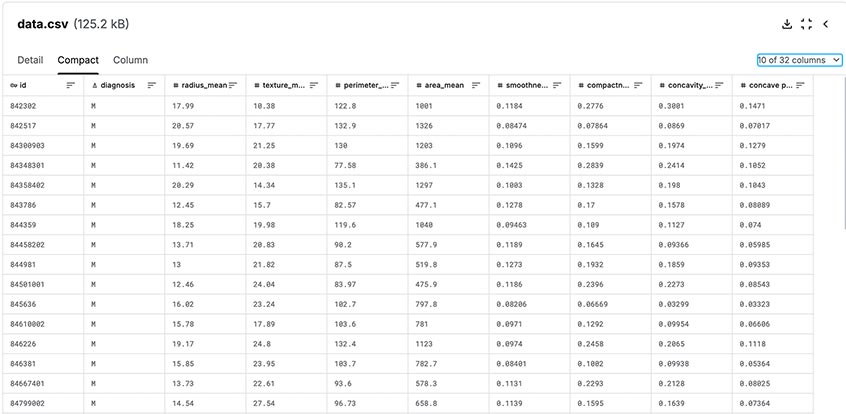
At Cloudstartuptech, we specialize in turning datasets into powerful machine learning solutions through our structured
"Data-Model-Deploy" workflow. Using the Breast Cancer dataset as a demo, we showcase how raw data can be transformed into a fully operational
machine learning endpoint, accessible via a user-friendly web interface. This end-to-end process ensures scalability, cost efficiency, and
rapid deployment tailored to your needs.
We take you data
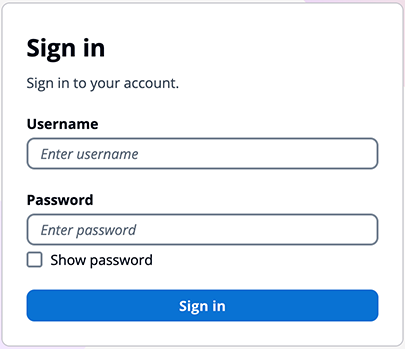
We create a Machine Learning model,and deploy it with Secure Authentication
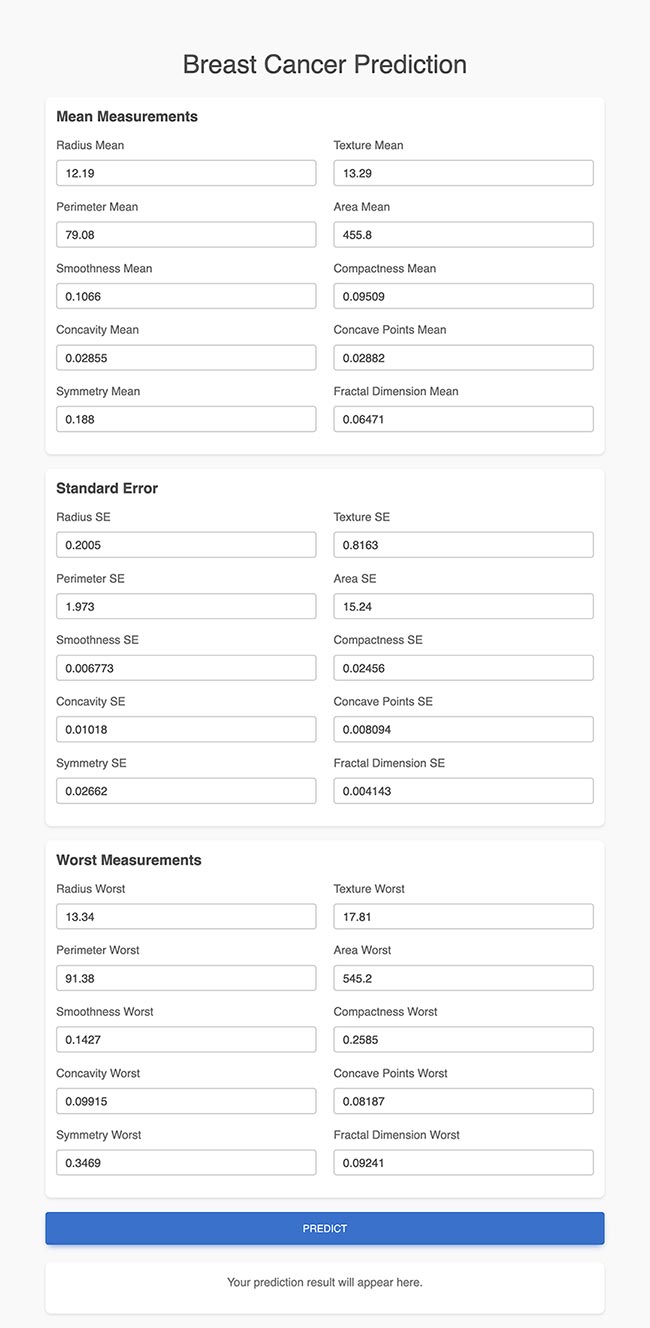
Develop a Web UI
Live demo click here
Summary of demo ML process
Model Assessment
This model results of the baseline model prior to optimisation :
Accuracy: 0.8823529411764706
Precision: 0.9230769230769231
Recall: 0.75
F1 Score: 0.8275862068965517
DEPLOYING A SECURE, SERVERLESS ML ENDPOINT WITH AUTHENTICATION
The use of AWS cloud-based XGBoost for generating high-quality baseline models proves to be highly effective, as evidenced by the model assessment results. AWS XGBoost leverages distributed computing power and optimized infrastructure to efficiently handle large datasets and complex computations, enabling rapid experimentation and tuning. The baseline model achieved an impressive accuracy of 88.2% and a high precision of 92.3%, demonstrating its ability to make reliable predictions. While the recall of 75% indicates some room for improvement in capturing all positive cases, the overall F1 score of 82.8% highlights a balanced performance between precision and recall.
In addition to robust machine learning capabilities, security remains a top priority in deploying AI-driven solutions. By integrating authentication and access control mechanisms, we ensure that sensitive ML endpoints remain protected while enabling authorized users to interact with the system efficiently.
1. Data: Preparing the Breast Cancer Dataset for Machine Learning
The journey begins with understanding and preparing the dataset to ensure it is clean, actionable, and ready for modeling.
Steps:
- Exploratory Data Analysis (EDA): The dataset was analyzed to identify patterns, distributions, and missing values.
Visualizations like histograms and scatter plots revealed key insights into features such as mean radius, texture, and diagnosis labels.
- Data Preprocessing: Missing values were addressed, numerical features normalized, and categorical variables encoded
for compatibility with machine learning algorithms.
- Feature Engineering: Additional features were derived from the dataset, such as creating interaction terms and applying dimensionality
reduction to improve model performance.
Outcome: A structured, optimized dataset ready for the next stage of the workflow.
2. Model: Building and Validating the Predictive Model
With the dataset prepared, the next step was to train and validate a machine learning model capable of making accurate predictions.
Steps:
- Model Training: The dataset was used to train an XGBoost model, selected for its ability to handle structured data effectively.
The model learned to classify tumors as "Malignant" or "Benign" based on input features.
- Hyperparameter Tuning: The model’s performance was optimized by fine-tuning parameters such as learning rate and max depth, ensuring
a balance between accuracy and efficiency.
- Model Evaluation: Metrics like accuracy, precision, recall, and F1-score were calculated to validate the model’s performance.
These metrics ensured that the model was reliable and free from significant biases.
Outcome: A validated machine learning model capable of delivering high-quality predictions.
3. Secure Deployment: Serverless ML Endpoint with Authentication
The final stage involved deploying the model as a secure serverless endpoint, paired with a static web interface for seamless and protected user interaction.
Steps:
- Serverless Endpoint: The trained XGBoost model was deployed as a serverless API using AWS Lambda, ensuring scalability and
cost efficiency. This endpoint processes requests and provides predictions in real-time.
- API Gateway Integration: API Gateway was configured to secure the endpoint, enabling controlled access, monitoring, and auditing
of prediction requests.
- Authentication with AWS Cognito: A user authentication system was implemented using AWS Cognito, providing secure access
control for the ML endpoint. OAuth 2.0 and OpenID Connect protocols ensure strong authentication while enabling features like Multi-Factor Authentication (MFA).
- Static Web UI with Secure Access: A serverless static website was deployed via Amazon S3 + CloudFront, enabling users to
interact with the model through a secure login. The authentication system ensures only authorized users can access prediction functionalities.
Outcome: A scalable, secure, and user-friendly ML deployment, ensuring both performance and compliance with data protection regulations.
Why Secure Authentication Matters for ML Deployment
- Enhanced Security: Unlike traditional authentication, which relies on static passwords, our approach uses token-based authentication
for secure, time-limited access.
- Role-Based Access Control (RBAC): Ensures that only authorized users can access sensitive ML predictions, mitigating security risks.
- Data Privacy & Compliance: Authentication ensures compliance with GDPR, HIPAA, and other security frameworks by limiting access to protected health information (PHI).
- Seamless User Experience: AWS Cognito allows Single Sign-On (SSO) and MFA, ensuring frictionless yet secure authentication.
- Reduced Attack Surface: Hosting the UI as a static website eliminates the need for traditional backend servers, reducing exposure
to vulnerabilities such as SQL injection and brute-force attacks.
- Secure API Gateway Integration: All prediction requests are authenticated and logged, ensuring traceability and security monitoring.
Final Thoughts
By leveraging Cloudstartuptech’s secure ML deployment framework, organizations can confidently deploy AI-driven applications without compromising security.
Whether for healthcare, finance, or research, our end-to-end solution provides seamless authentication, serverless scalability, and a user-friendly interface.
This ensures that AI-powered insights remain accessible, protected, and optimized for real-world applications.